The cryptocurrency exchange Kraken reported an extortion attempt that once again demonstrated how thin the line can be between security research and outright abuse.

According to the company, one of the researchers discovered a vulnerability in the system related to the mechanism for crediting funds to user accounts. At first glance, this appears to be a technical detail, but it is precisely such “details” in the crypto industry that often become entry points for serious attacks.
The essence of the vulnerability was that under certain conditions it was possible to artificially create a balance on an account — essentially to “draw” funds that were not backed by real assets. This did not mean direct access to the exchange’s reserves, but it created the illusion of available funds in the user interface.
And this is where things become most interesting. Instead of following the standard procedure of responsible disclosure through a bug bounty program, the researcher chose a different path. He attempted to use the discovered issue as a tool of pressure, demanding a reward under the threat of public disclosure.
From an industry perspective, this is a fundamental point. Bug bounty programs exist precisely so that “white hat” hackers can safely and legally report discovered vulnerabilities and receive compensation for it. But the key word here is “safely.” Any attempts at pressure, blackmail, or threats automatically move the situation from the category of cooperation into the category of wrongdoing.
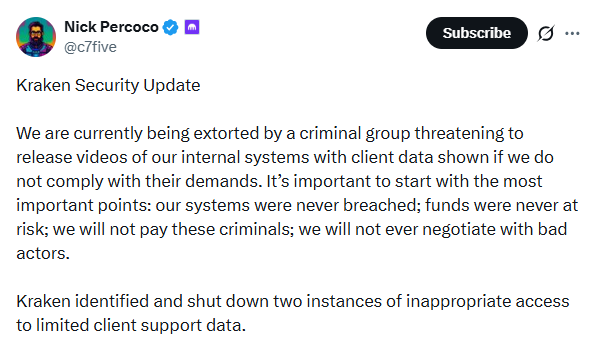
Kraken explicitly stated that it considers the researcher’s actions to be extortion. In response, the company promptly initiated an internal investigation, fixed the vulnerability, and notified law enforcement authorities.
It is important to note that despite the potential seriousness of the issue, users’ real funds were not affected. This is perhaps the key element of the entire story. The reason lies in the system architecture. Even if a “fake” balance could be displayed in the user interface, it did not allow actual withdrawal of funds. There are multiple layers of verification between the display of numbers on the screen and the actual movement of assets.
Kraken emphasizes that its asset storage system is built on a multi-layered principle. Access to funds is restricted, transactions проходят through independent verification mechanisms, and any anomalous actions are automatically detected and blocked. This means that even if there is a vulnerability at the level of user balance accounting, access to reserves remains protected.
Thanks to this architecture, the attacker was unable to turn the scheme into real financial losses. He could manipulate the display, but could not convert it into withdrawals. Nevertheless, the incident raises a deeper issue that goes beyond a single platform.
The crypto industry has historically faced the problem of discrepancies between the “displayed” and “actual” state of assets. The interface may show one thing, while the actual reserves are something else. During periods of high load or in complex system architectures, such discrepancies can become starting points for attacks.
From the perspective of data analysis and system architecture, such vulnerabilities more often indicate not a classic “security hole,” but challenges in synchronizing internal accounting mechanisms. This is a subtle but critically important area — where the interface, the database, and real assets intersect.
Even if direct access to funds is impossible, such errors can affect liquidity, user behavior, and trust in the platform. Imagine a situation where funds “appear” in accounts — this could trigger a chain of actions that, under other conditions, might lead to systemic risk.
That is why such incidents are taken seriously by the market, even if they did not result in losses. The issue of trust also deserves special attention. Kraken specifically noted that it is ready to pay substantial rewards for critical findings, but only if a transparent and proper procedure is followed. In this case, the company refused to meet the demands because they amounted to blackmail. This is an important signal for the entire industry: the boundaries of acceptable behavior in cybersecurity remain clear despite the specifics of the crypto market.
In a broader context, this story shows where the industry is heading. If earlier the main focus was on protecting assets, now transparency of internal processes is coming to the forefront. Users need not only to know that their funds are protected, but also to understand how the accounting system actually works.
A logical question arises: will crypto platforms be able to make their internal mechanisms so transparent and verifiable that even the theoretical possibility of such situations is eliminated? For now, the answer is unclear. But one thing is already evident: the next stage of competition between exchanges will be not only for liquidity and fees, but also for trust — the most scarce resource in the crypto industry.
All content provided on this website (https://wildinwest.com/) -including attachments, links, or referenced materials — is for informative and entertainment purposes only and should not be considered as financial advice. Third-party materials remain the property of their respective owners.


