The story of the arrest of a member of an international hacker group in Ukraine is not just another episode of cybercrime, but a clear example of how digital attacks are turning into a full-fledged transnational business with hundreds of millions of dollars in turnover and a complex infrastructure ranging from intrusion to money laundering.
According to law enforcement agencies, the network systematically targeted companies in Europe and the United States, using malicious software to steal confidential data. The scenario is classic, but no less effective: after breaching victims’ systems, the attackers copied internal documents, databases, and corporate communications, and then demanded ransom for their return or non-disclosure. In essence, this is a combination of ransomware and data extortion, which significantly increases the likelihood of payment from affected companies.
The estimated damage – more than $100 million – illustrates the scale of the operation. These are no longer “lone hackers” but a structured group with role distribution, where some are responsible for the technical side of attacks, others for negotiations with victims, and others for financial flows and subsequent laundering.
The suspect arrested in Ukraine, according to the investigation, handled one of the key functions – the withdrawal and “cleaning” of funds. Money obtained as ransom was first accumulated in controlled crypto wallets, then passed through a chain of transactions designed to obscure tracing. After that, funds were partially cashed out and invested in real-world assets such as real estate, vehicles, and other property in Ukraine. This is a typical “from digital to physical” scheme, where virtual assets are converted into tangible value that is harder to link to the original source.
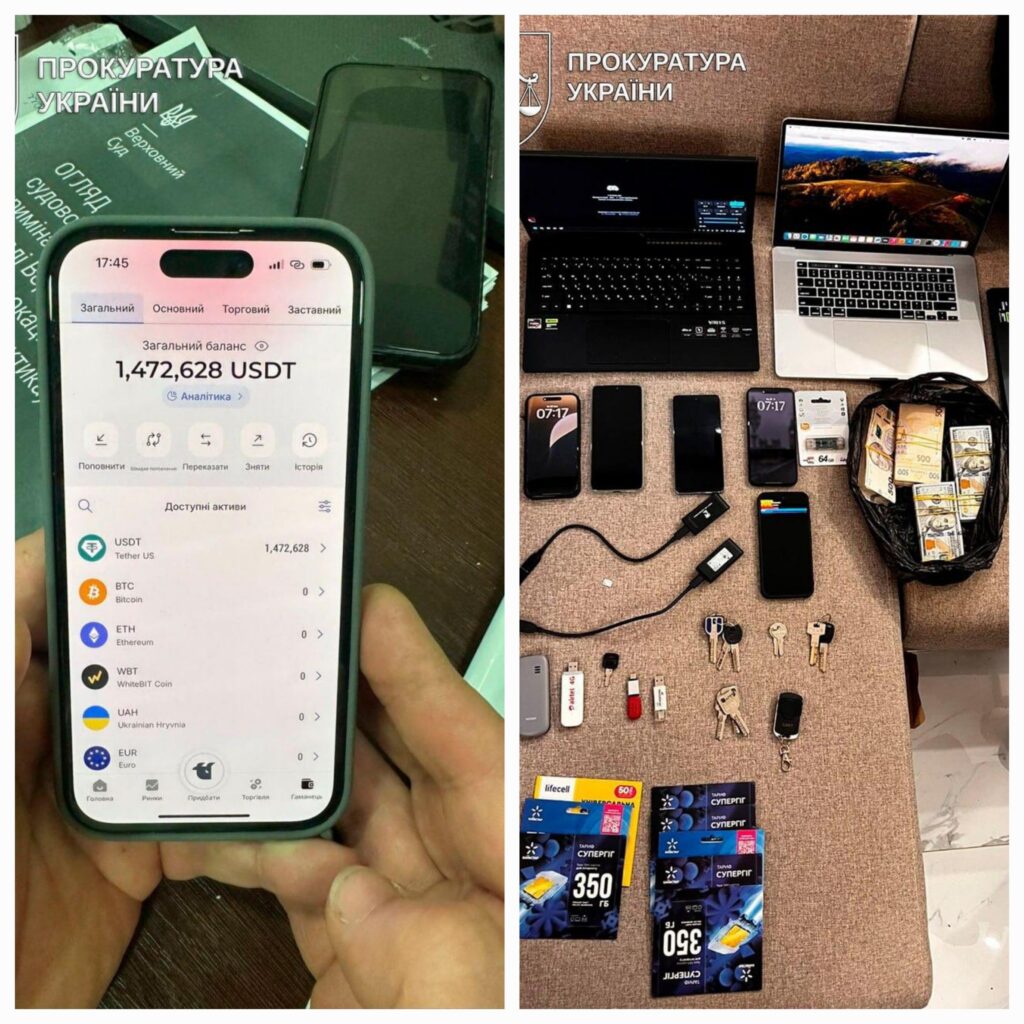
The scale of investigative actions confirms the seriousness of the case. More than 30 searches allowed authorities not only to detain the suspect but also to uncover significant assets. Seized property includes residential houses, apartments, vehicles, around $1 million in cash, and approximately $8.3 million in cryptocurrency. The total value of seized assets is estimated at more than 80 million hryvnia.
It is also worth noting that this is not the first suspect in the case. Earlier, one of the organizers, who was hiding abroad, as well as another participant in the scheme, were already formally charged. This indicates a phased dismantling of the entire network rather than an isolated arrest.
According to Prosecutor General Ruslan Kravchenko, investigators are continuing to identify other involved individuals. The court has already ordered pre-trial detention for the suspect, with bail set at 399 million hryvnia – a figure that in itself reflects the scale of the alleged operations.
It is important to understand that such cases now sit at the intersection of several domains – cybersecurity, financial monitoring, and international law. Attacks are carried out in one jurisdiction, victims are located in another, and funds pass through a third, often using cryptocurrencies originally designed as decentralized instruments.
At the same time, the laundering scheme shows that cryptocurrency is no longer the “final destination” for criminal proceeds. Instead, it has become an intermediate layer – a convenient tool for fast movement of funds, but not for long-term storage. Ultimately, the money still returns to the traditional economy through asset purchases.
This case also demonstrates that law enforcement agencies are gradually adapting to new realities. While tracking crypto transactions was considered extremely difficult just a few years ago, today analytical tools and international cooperation make it possible to reconstruct transaction flows and identify specific participants.
In a broader sense, this is a signal for businesses: cyber threats are no longer just an IT issue but a full-scale financial risk. Companies pay ransoms not because it is convenient, but because the damage from data leaks can be even greater. As a result, such groups will continue to exist as long as the economic model remains one where attacks are profitable.
And perhaps the main takeaway from this story is that digital crime is becoming increasingly “traditional” in nature. Behind complex schemes, crypto wallets, and malware lie very familiar goals: money, assets, and their legalization. Only the tools have become more modern, while the scale has grown significantly.
All content provided on this website (https://wildinwest.com/) -including attachments, links, or referenced materials — is for informative and entertainment purposes only and should not be considered as financial advice. Third-party materials remain the property of their respective owners.


