In recent months, blockchain infrastructure analysts have recorded a noticeable increase in so-called “address poisoning” attacks on the Ethereum network. This refers to an old but recently rapidly scaling fraud scheme that exploits user behavior patterns, cryptocurrency wallet interfaces, and the transparency of blockchain transactions.
According to analytical services and blockchain explorers, after the network upgrade known as Fusaka, the cost of executing transactions dropped sharply. Lower fees made it possible to conduct mass distribution of so-called dust transactions. As a result, the number of fake transfers of the Tether (USDT) stablecoin increased by approximately 612%.

At first glance, such transfers may appear harmless. They involve transactions with zero or almost zero value. However, they are used by attackers as a tool for carrying out one of the most widespread and least noticeable attacks against cryptocurrency users.
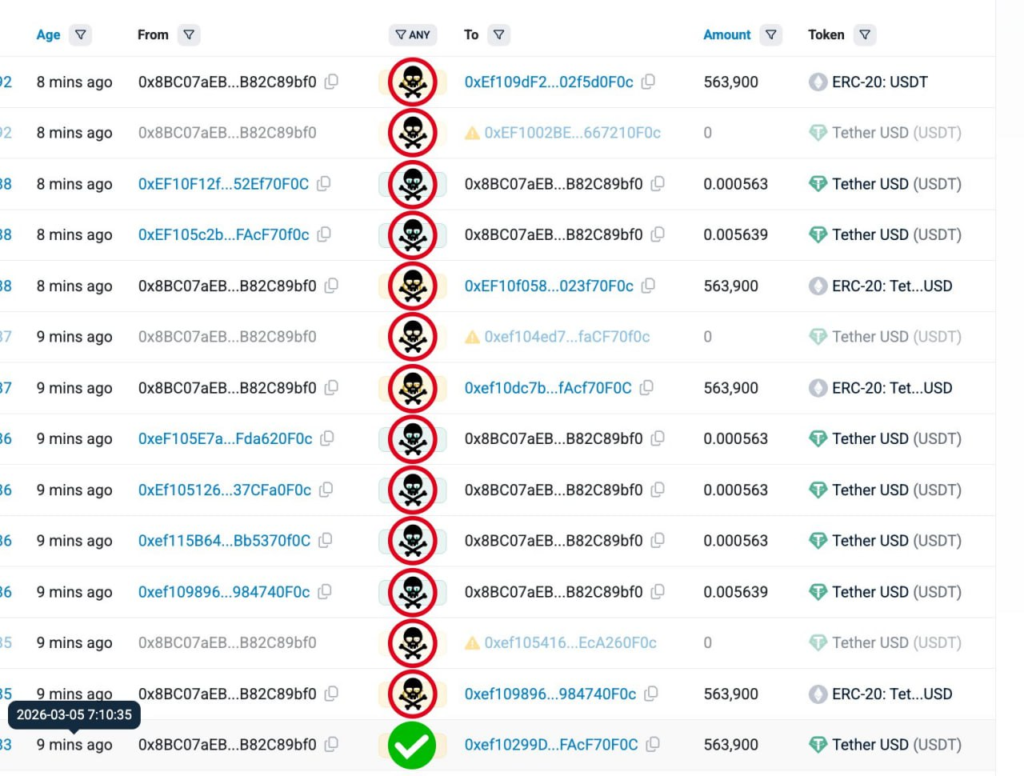
The essence of the scheme is quite simple but extremely effective. Fraudsters create cryptocurrency addresses that visually resemble addresses the user has previously interacted with. Typically, they copy the first and last characters of the address, since these fragments are most often displayed in cryptocurrency wallet interfaces and blockchain explorers.
After creating such a “clone,” the attacker sends a microtransaction or zero-value transfer to the address of the potential victim. As a result, this fake address appears in the user’s transaction history.
The problem arises when the wallet owner wants to send funds again to a familiar address. Many users copy the address directly from the list of previous transactions. If the attacker’s address is already present in the history and visually almost indistinguishable from the real one, the user may mistakenly copy it.
The difference between the addresses often consists of only a few characters in the middle of a long string. Considering that cryptocurrency addresses can contain dozens of characters and some wallets display them in a shortened format, noticing the substitution can be extremely difficult. As a result, the user voluntarily sends funds to the fraudster’s address, believing that the money is being transferred to a familiar wallet.
According to blockchain infrastructure analytics and explorers such as Etherscan, between July 2022 and June 2024 about 17 million attempts of such attacks were recorded. Total user losses are estimated at approximately 79.3 million dollars.
Interestingly, the effectiveness of such attacks in terms of successful cases is relatively low. The success rate is estimated at around 0.01 percent. However, the scale of the operation makes it highly profitable for attackers.
Fraudsters operate using industrial methods. Special algorithms and software are used to generate similar addresses. Such programs automatically create thousands and even millions of addresses that match key visual fragments of popular wallets or addresses of well-known services. After that, automated scripts begin mass distribution of microtransactions to network users. Thanks to low fees, the cost of such attacks is minimal, while the potential profit can be quite significant.
Such schemes are especially активно used with popular tokens and stablecoins. Among them, Tether appears most frequently because it is widely used for trading operations and transfers between exchanges and wallets. At the same time, attacks of this type are not limited only to the Ethereum network. They can occur in virtually any public blockchain network with high user activity.
Similar schemes are periodically recorded in the Bitcoin network as well, but due to higher fees such attacks occur there much less often. The high cost of transactions significantly reduces the economic attractiveness of mass distributions.
Attacks are much more common in networks with low fees and a large number of users. Among them are TRON and Polygon. In such networks attackers can send huge volumes of microtransactions with almost no significant costs. In essence, the key factor here is not the blockchain technology itself but the economic model of the network. The cheaper it is to send transactions, the easier it becomes to carry out mass attacks of this type.
In recent years experts have increasingly said that address poisoning is gradually turning into an industry. Automation of processes, the use of specialized software, and the scale of operations allow attackers to operate almost like full-fledged digital enterprises.
Another problem is that such attacks are difficult to prevent at the blockchain network level itself. By its nature blockchain is an open system in which any user can send a transaction to any address. Restricting such activity without changing the fundamental principles of how the network operates is practically impossible.
Therefore, the main responsibility for protecting users lies with developers of wallets and interfaces of cryptocurrency services. Many of them have already begun implementing additional security mechanisms.
For example, some wallets warn the user if an address was recently added to the transaction history or looks suspicious. Other services implement algorithms that analyze address similarity and signal a potential substitution. Nevertheless, the problem has not yet been fully eliminated. The human factor remains the main weak point of the system.
Experts recommend always checking the full address before sending cryptocurrency, especially if it is copied from transaction history. It is safest to use saved address books, QR codes, or verified contacts in wallets. In addition, it is useful to check not only the first and last characters of the address but also several characters in the middle of the string. This is where substitutions are most often hidden.
The mass spread of address poisoning attacks shows how important the issue of user interface security is becoming in the cryptocurrency industry. Blockchain technology ensures transparency and immutability of transactions, but it does not protect users from human mistakes. That is why as cryptocurrencies become more popular increasing attention is being paid not only to cryptographic security mechanisms but also to interface design that should minimize the likelihood of such errors.
For now, attacks of this type remain one of the most widespread forms of fraud in the cryptocurrency environment. And the cheaper transactions become in blockchain networks, the higher the probability that the scale of such operations will continue to grow.
All content provided on this website (https://wildinwest.com/) -including attachments, links, or referenced materials — is for informative and entertainment purposes only and should not be considered as financial advice. Third-party materials remain the property of their respective owners.


