The Federal Bureau of Investigation has launched a large-scale investigation after malicious software was discovered in several computer games distributed through the popular gaming platform Steam, owned by Valve Corporation. According to the agency, attackers used the gaming ecosystem as a channel to spread malware by disguising it as ordinary game projects.
According to investigators, potentially infected applications may have been downloaded by thousands of users. The FBI has urged anyone who installed suspicious games to contact the agency and participate in the investigation. Representatives of the bureau emphasized that their main task is to identify all victims and determine the technical mechanisms used to infect devices. This is necessary not only to find the organizers of the cyberattack but also to prevent similar incidents in the future.
Games as a cyberattack tool
Preliminary data suggests that the malware was distributed through several games published in the Steam catalog. Some of them appeared to be fully functional game projects: they could run normally and included gameplay mechanics, graphics, and user interfaces, but at the same time they executed hidden processes on users’ computers.
The list of suspicious projects includes:
- BlockBlasters
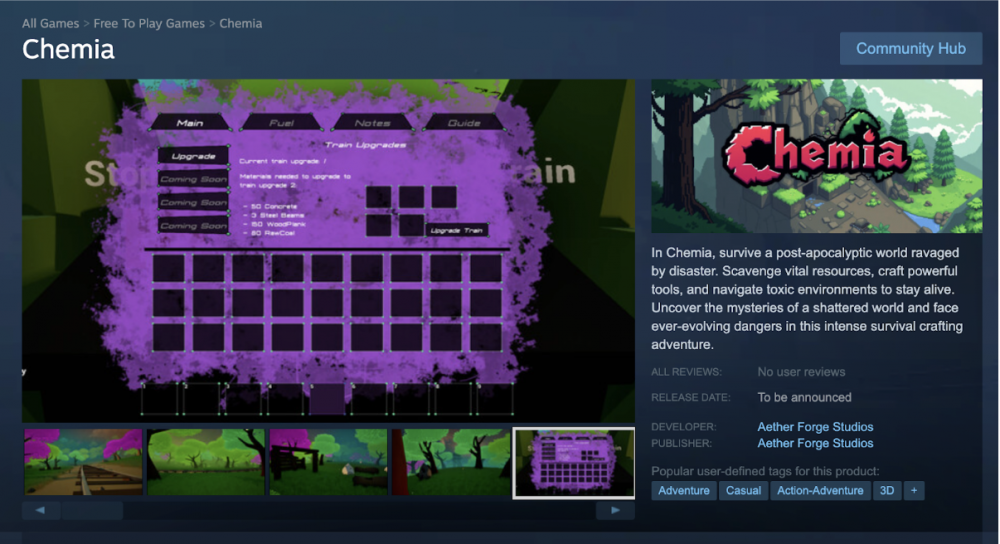
- Chemia
- Dashverse
- DashFPS
- Lampy
- Lunara
- PirateFi
- Tokenova
Investigators note that some of these applications may have been used as so-called “decoy products.” Their primary purpose was not entertainment but the distribution of malicious code. After installation, such programs could perform various hidden actions:
- steal user credentials;
- gain access to files on the computer;
- install additional malicious modules;
- collect information about cryptocurrency wallets and access keys;
- intercept browser and payment system data.
Particular attention is being paid to the games Chemia and PirateFi. These projects were removed from Steam in the summer of 2025 after cybersecurity specialists discovered suspicious code in them. Analysis showed that the malware in these applications could steal data related to digital assets, including information about cryptocurrency wallets and private keys.

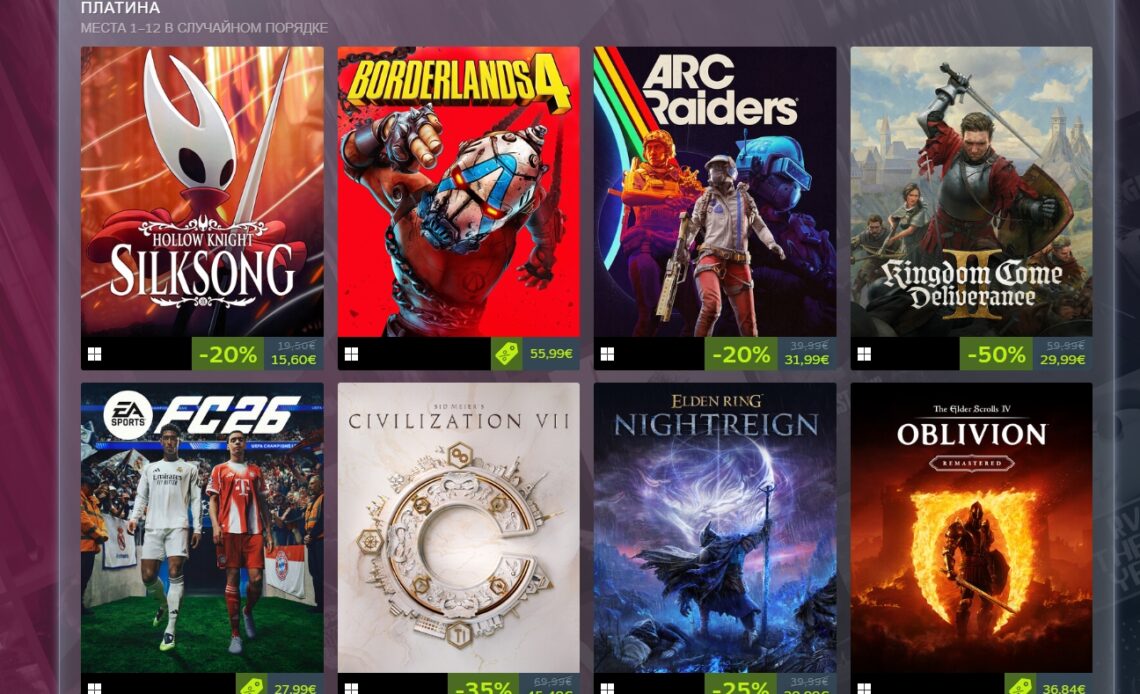
Why Steam
The Steam platform remains one of the largest digital ecosystems for distributing computer games in the world. According to Valve, in 2025 the service had around 132 million active users per month. The platform’s catalog includes more than 117,000 games of various genres and complexity levels, ranging from large projects by world-class studios to small indie developments.
The enormous scale of the platform and its open publishing system make it attractive to cybercriminals. Despite the presence of security checks, new games regularly appear in the catalog, giving attackers the opportunity to disguise malicious programs as independent game projects.
Experts note that attackers often use several stages to introduce malicious code. First, a relatively simple game without malicious components is published so that it passes moderation and gains the trust of users. Later, a malicious module is added in one of the updates and begins spreading among players.
Interest in cryptocurrencies as the main target
According to cybersecurity specialists, most such attacks are aimed at gaining access to users’ digital assets. In recent years, cryptocurrencies have become one of the main targets for cybercriminals because stolen funds can be quickly transferred through blockchain networks and transaction traces can be concealed.
Many malware programs specifically search a computer for:
- cryptocurrency wallet files;
- browser extension data used for storing crypto assets;
- seed phrases and private keys;
- configuration files of popular crypto wallets.
If such data is found, the program sends it to attackers’ servers, after which funds can be withdrawn from victims’ wallets.
Gamers as an easy target
Experts emphasize that the gaming community has long been one of the main targets for cybercriminals. There are several reasons for this. First, gamers often install a large number of programs, modifications, and add-ons. Second, many players use third-party tools to improve gameplay, such as mods or cheat programs.
Such files are often distributed through unofficial websites and forums where security control is practically absent. This creates ideal conditions for the deployment of malicious code. For example, specialists previously discovered malware in a fan-made game based on the popular series Super Mario. In another case, malicious code was distributed through cheat programs for the military shooter series Call of Duty.
After installation, such programs could intercept user data, install hidden cryptocurrency miners, or steal funds from crypto wallets.
Authorities’ response and possible consequences
The FBI stated that the investigation is still in its early stages, but authorities are already considering the possibility that an organized cybercriminal group may be involved. Investigators are analyzing the servers through which the malware was distributed and examining network logs and digital traces left by the programs.
Agency representatives also reminded users that victims of such attacks may have the right to compensation and other forms of support under federal law. To qualify, it is necessary to officially report the infection of a device or the loss of digital assets.
A broader trend
The case of malicious games on Steam is part of a broader trend. According to cybersecurity analysts, the number of attacks targeting gamers and cryptocurrency users is constantly increasing. The more popular digital assets and gaming platforms become, the more often they attract the attention of cybercriminals. Experts warn that users should be cautious when installing new games and software, especially if they come from little-known projects or request unusual permissions during installation.
The investigation is ongoing, and the FBI does not rule out that the list of infected games and potential victims may expand significantly as new data is analyzed. In the meantime, specialists recommend that users scan their devices with antivirus tools, keep their software updated, and carefully monitor the security of cryptocurrency wallets and accounts.
All content provided on this website (https://wildinwest.com/) -including attachments, links, or referenced materials — is for informative and entertainment purposes only and should not be considered as financial advice. Third-party materials remain the property of their respective owners.