Cryptocurrency exchange has long ceased to be a niche activity for enthusiasts and has become a full-fledged element of the financial system. Today, users exchange digital assets through P2P platforms, Telegram channels, private brokers, and even during in-person meetings. However, along with growing popularity, the darker side of the market is also expanding — fraud, which is becoming increasingly sophisticated and widespread.
According to the Chainalysis 2026 report, losses from crypto fraud reached 17 billion dollars in 2025. In particular, impersonation schemes, where criminals pose as support services, surged dramatically — their number increased by 1400 percent. At the same time, the use of artificial intelligence has made fraudulent operations several times more effective than traditional methods. This highlights a simple reality: the market is evolving, but so are the risks.
The main reason for this vulnerability lies in the very nature of cryptocurrencies. Transactions are irreversible. If funds are sent to the wrong address, it is almost impossible to recover them. In traditional banking, there are mechanisms to reverse or dispute transactions, but in crypto, responsibility lies entirely with the user. Add to this the growth of P2P exchanges, where deals often occur without clear rules or guarantees, and you get an ideal environment for scammers. New users are particularly vulnerable, as they are just entering the space and are not yet familiar with common fraud schemes.
Despite the technological complexity of the crypto market, most scam schemes remain surprisingly simple. They rely on urgency, trust, and inattention.
One of the most common schemes is phishing clones of exchange platforms. Scammers create websites that are nearly identical to legitimate ones. Users land on these sites through ads or messenger links, enter their data, and effectively hand it over to criminals. The difference may be just one character in the domain name, but the cost of the mistake is the loss of funds.
Another frequent scenario is the substitution of payment details during communication. A deal is discussed in a chat, everything appears normal, but at the last moment the “counterparty” claims that the wallet has changed. If the user does not verify the information, the crypto is sent to the wrong address. This tactic works precisely because it occurs when the user is already psychologically ready to complete the transaction.

Another popular method is fake payment confirmations. The user receives a screenshot of a supposedly completed transfer and is pressured to act quickly: the money is “on the way,” so send the crypto immediately. In reality, no payment has been made. The key rule here is simple: only actual receipt of funds or a confirmed blockchain transaction counts as proof — not a screenshot.
A separate category of risks involves the substitution of wallet addresses and QR codes. Users may receive an address that looks correct but actually belongs to a scammer. This can happen through malicious extensions or clipboard manipulation. A simple check of the first and last characters of the address can often prevent losses, yet many users ignore it.
There are also more subtle schemes, such as exchange rate manipulation. A user is offered a favorable rate, but after sending funds, additional fees appear or terms change. As a result, the final amount received is significantly lower than expected. This is not outright fraud, but exploitation of unclear or unfixed transaction terms.
With the growing popularity of crypto, fake support services are becoming more common. Scammers contact users pretending to represent a platform, report a “problem,” and request access to wallets, seed phrases, or verification codes. In reality, this is an attempt to take full control of the funds. The rule is simple: no legitimate service will ever ask for such data.
Special attention should be given to “guarantor” schemes. A third party is introduced into the chat as someone who supposedly controls the transaction. In practice, this person is often part of the scam. The user believes they are protected, but in fact, they are handing over funds to fraudsters.
Technical aspects are also exploited. For example, network or token substitution. Users may be asked to send assets via a different network, resulting in lost funds or extremely difficult recovery. This is especially relevant for tokens like USDT, which exist across multiple networks.
Offline exchanges, which may seem safer to some, also carry risks. During in-person meetings, issues such as incorrect cash counting, counterfeit bills, or pressure to rush the process can arise. These are classic “old world” scams, simply adapted to a new environment.
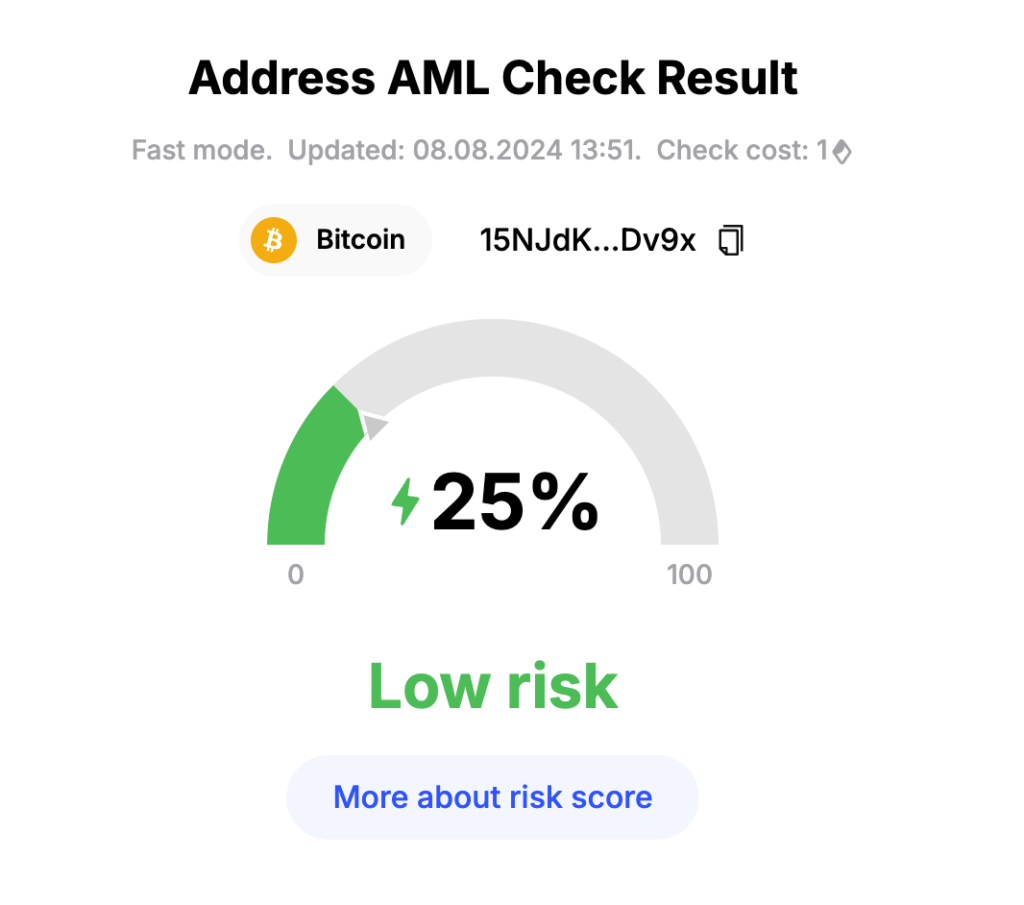
Finally, one of the most cynical schemes is the fake AML check. After receiving funds, the user is told that the transaction has been “blocked” and is asked to pay an additional fee to unlock it. This is a completely fabricated mechanism, but it works because it sounds plausible in the context of real discussions about regulation and anti-money laundering.
It is important to understand that all these schemes share one common feature — they do not require complex technology. Scammers rely not on hacking, but on human behavior. Urgency, trust, the desire for a better rate, and fear of missing out are their main tools.
In 2026, safe crypto exchange is less about choosing the right platform and more about discipline. Verifying addresses, fixing transaction terms, avoiding haste, and ignoring any “urgent” requests are basic principles that work better than any complex strategy.
The crypto market continues to grow and attract new participants. But along with opportunities comes responsibility. And if раньше говорили “not your keys — not your coins,” today it can be extended: if you didn’t verify the details, the money is no longer yours.
All content provided on this website (https://wildinwest.com/) -including attachments, links, or referenced materials — is for informative and entertainment purposes only and should not be considered as financial advice. Third-party materials remain the property of their respective owners.


