Scammers are increasingly selling fake hardware wallets with pre-set seed phrases – and this is one of those schemes where no actual hacking takes place. The user, with their own hands, “sets up” a device that is designed from the start not to protect funds, but to steal them.
According to Kaspersky, this is a new wave of attacks related to supply chain compromise. This is no longer just phishing websites or malicious links – attackers are going deeper and interfering at the level of the physical device. Fake hardware wallets are almost indistinguishable from the originals: the same packaging, the same design, the same logos. Sometimes they even create the illusion of a “sealed” product. But inside – modified components or altered firmware that makes the device vulnerable from the very first use.
The key element of the scheme is a pre-generated seed phrase. In a normal situation, the seed phrase is generated by the device itself during the initial setup, and only the user has access to it. In the case of fakes, everything happens the other way around: the phrase is already “prepared” in advance and known to the attackers. Users may be given a “ready-made” card with the seed phrase or shown it during setup as if it were a standard step. Sometimes this is even presented as a convenience – as if “everything has already been simplified for you.”
In practice, this means that the moment a person transfers funds to such a wallet, those funds are already under the control of a third party. The theft may not happen immediately – which makes the scheme even more dangerous. The funds may sit for days or weeks, creating an illusion of safety, and then suddenly disappear. Without warning, without the possibility of reversal, without any chance of recovery.
Particularly alarming is the fact that these fakes affect multiple well-known brands. This indicates the scale of the problem and shows that attackers are operating systematically rather than sporadically. In essence, this is a full-scale attack on trust in hardware wallets as a class of devices.
There are several warning signs to watch for. First, any “ready-made” seed phrase is an immediate red flag. A legitimate wallet is never shipped with a pre-generated phrase. Second, suspicious packaging – damage, signs of tampering, or inconsistencies with the original. Third, an unusual setup process – if the device behaves differently from the manufacturer’s instructions, it is better to stop.
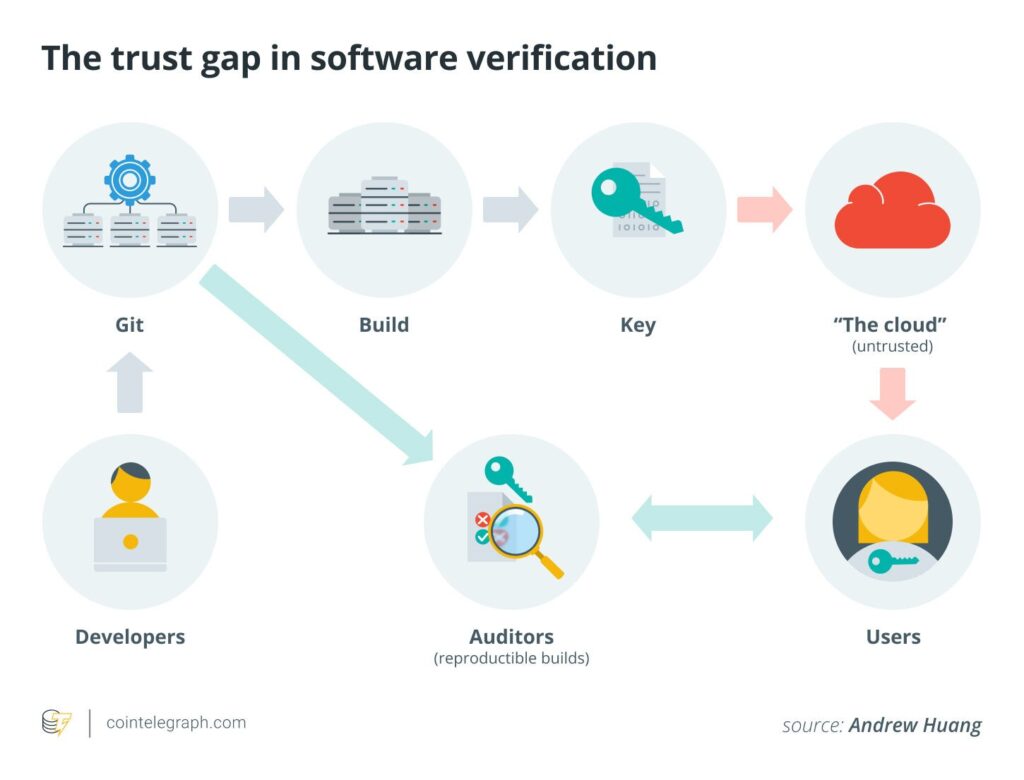
It is important to understand a simple point: the security of a hardware wallet depends not only on technology, but also on trust in the source of the device. Even the most advanced security features – such as cryptographic firmware verification – only work if the device itself is genuine. If the foundation is already compromised, no protection will help.
That is why the basic rule remains as old as a good bank vault: buy such devices only from official manufacturers or authorized sellers. No “great deals,” no “almost original but cheaper” options. In crypto, such compromises tend to end the same way.
And the second rule, no less important: the seed phrase must be generated only by you and only on the device during the initial setup. No one should know it, see it, or “prepare” it in advance. If this condition is violated, you are not dealing with a security tool, but with a ready-made theft mechanism.
In the end, the conclusion is quite harsh but honest. In the world of cryptocurrencies, security is not only about technology, but also about discipline. And sometimes the most dangerous “hack” is the one you initiate yourself by trusting the wrong device.
All content provided on this website (https://wildinwest.com/) -including attachments, links, or referenced materials — is for informative and entertainment purposes only and should not be considered as financial advice. Third-party materials remain the property of their respective owners.


