Cybersecurity specialists warn about a new scheme for hacking accounts in WhatsApp that is spreading quickly and has already led to a large number of compromised user accounts. The peculiarity of this scheme is that it barely resembles traditional cyberattacks. The user does not receive direct threats, does not install malicious software and does not see obvious signs of a hack. Everything looks like an ordinary everyday situation, which is why many people do not perceive what is happening as a danger.
Usually everything begins with small details. A person receives several strange calls from unknown numbers. They may arrive one after another or with short intervals. The user usually simply rejects the calls or ignores them, considering them ordinary spam. Sometimes after a series of calls a message arrives in WhatsApp. It may look completely harmless. In some cases the message comes from an unknown number, sometimes from a contact that exists in the phone book, and sometimes it is disguised as a message from support or a technical service. The text may ask the user to confirm a code, vote for someone, verify information or open a supposedly important link.
At first glance such messages look routine. People receive dozens of notifications and messages every day, so they do not always think about possible risks. This is exactly what the new scheme called Ghost Pairing relies on. Unlike classic attacks, it does not require installing viruses or malicious programs. Fraudsters use a standard WhatsApp feature designed to connect additional devices to one account.
The service allows the messenger to be used not only on a phone but also on a computer, tablet or another device. To do this, it is enough to link the device to the main account. When the user confirms the connection or enters a special code, the new computer or smartphone gains access to the user’s chats. This function was created for user convenience, however it is increasingly being used by attackers.

The attack scenario looks as follows. Fraudsters initiate the process of connecting their device to someone else’s account. To complete the procedure confirmation from the phone owner is required. The user receives a code or confirmation request and, not suspecting what is happening, enters it on a third-party website or confirms the request inside the application. At that moment the attacker’s device becomes linked to the victim’s account. Externally nothing changes for the phone owner. The messenger continues to work as usual, messages are received and sent, and no warnings appear. However another device is already connected to the account at the same time.
After that attackers gain access to a significant portion of personal information. They can read conversations, view photos and documents, see the contact list and the history of chats. Moreover they gain the ability to send messages on behalf of the account owner. For friends, relatives and colleagues such messages look completely authentic because they arrive from a real chat.
This is exactly what makes the scheme especially dangerous. Previously scammers tried to deceive people from unknown numbers, but now they can write on behalf of a real person. For example acquaintances may receive a message urgently asking to borrow money, transfer a small amount or help in some situation. Sometimes attackers send links asking people to vote for a child in a contest or to look at an important photo. Recipients trust such messages because they see a familiar name and a familiar conversation. As a result scammers may deceive several people at once using a single hacked account.
In addition to financial fraud such attacks may lead to other consequences. Access to conversations allows attackers to obtain personal data, work information, phone numbers and even details of a person’s everyday life. In some cases such information may be used for further attacks or blackmail.
The danger is increased by the fact that today WhatsApp has become one of the main communication channels. Through the messenger people discuss work issues, arrange meetings, solve everyday problems and communicate with relatives, doctors, teachers and colleagues. In fact a messenger account becomes part of a person’s digital identity. Losing control over it means not only losing conversations but also giving attackers the opportunity to act on behalf of the owner.
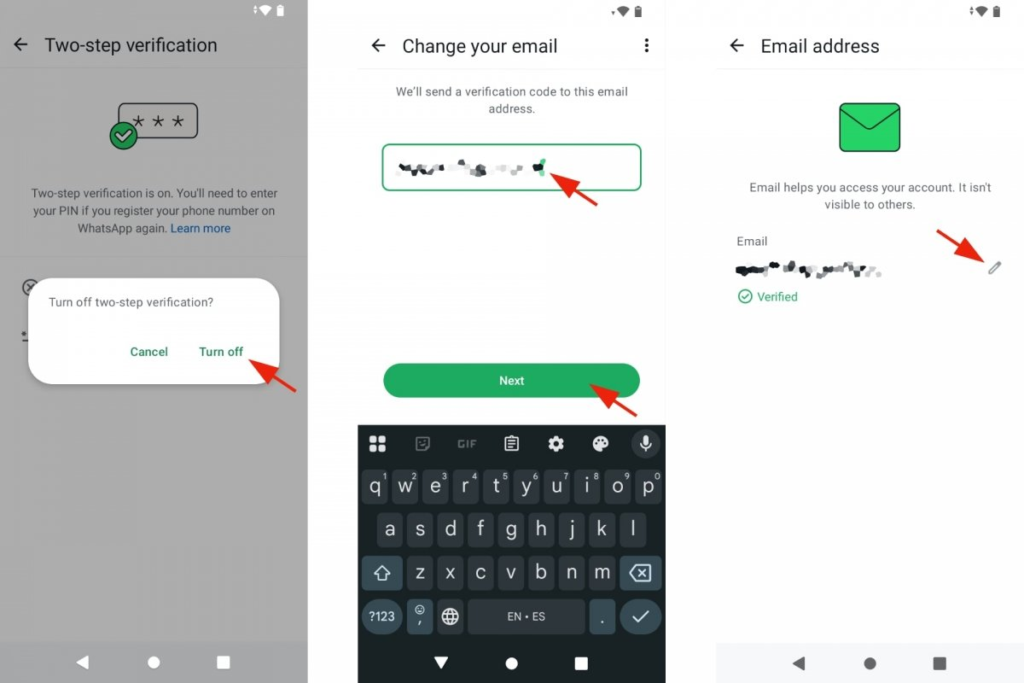
Cybersecurity specialists recommend several simple protection measures. First it is advisable to enable two-step verification in the WhatsApp settings. This feature adds an additional level of protection and requires entering a special PIN code when the account is registered again. It is also important to regularly check the section of connected devices. In the application settings there is a section called Linked Devices where all computers and devices that have access to the account are displayed. If an unknown device appears in the list it should be disconnected immediately.
Another important rule is never to enter WhatsApp verification codes on third-party websites and never share them with other people. Even if a message looks convincing or comes from a familiar contact, the verification code is intended only for the account owner. In addition specialists advise treating any links with caution, especially if a message contains a request to urgently confirm something or open a link.
Experts also emphasize that such schemes work not because users are careless. The modern flow of information is enormous and people constantly receive notifications, messages and calls. In conditions of hurry and fatigue it is easy to miss an important detail or automatically press a confirmation button. Attackers rely precisely on this human factor.
Therefore the main risk of such attacks is that a person may not suspect the hack for a long time. Sometimes users learn about the problem only after their acquaintances begin receiving strange messages from their name. By that moment scammers may already have access to conversations and contacts.
Specialists recommend periodically checking account settings and the list of connected devices. In WhatsApp this can be done through the Settings menu and then opening the Linked Devices section. All active connections are displayed there. If the list contains a device the user does not recognize it should be disconnected immediately and the security settings should be checked. Such a simple check can help detect unauthorized access in time and protect one’s digital identity.
All content provided on this website (https://wildinwest.com/) -including attachments, links, or referenced materials — is for informative and entertainment purposes only and should not be considered as financial advice. Third-party materials remain the property of their respective owners.


